- Home
- Hardware
- SDKs
- Cloud
- Solutions
- Support
- Ecosystem
- Company
- Contact
news
Espressif Sponsors the SHA2017 Badge Project
Shanghai, China
Jun 2, 2017
Espressif sponsors the SHA2017 International Hacking Festival by offering ESP-WROOM-32 for participants’ electronic badges.
SHA2017 (Still Hacking Anyway) is a non-profit, international, outdoor, hacker camp which will take place in the Netherlands this year, from August 4th until 8th. The festival is organized by volunteers, so it is a non-commercial, self-organized community event. A great number of talks, workshops and installations are included in the event’s programme.
At the center of all these are the festival’s core values: hacking, connecting with peers from around the globe, sharing knowledge with them, experimenting with technology and striving for innovation. According to the organizing committee, SHA2017 aims to attract a diverse crowd of “free-thinkers, philosophers, activists, geeks, scientists, artists, makers, creative minds, and others from all over the world to contemplate, reflect, share, discuss, criticize, look ahead, code, build, and more”.
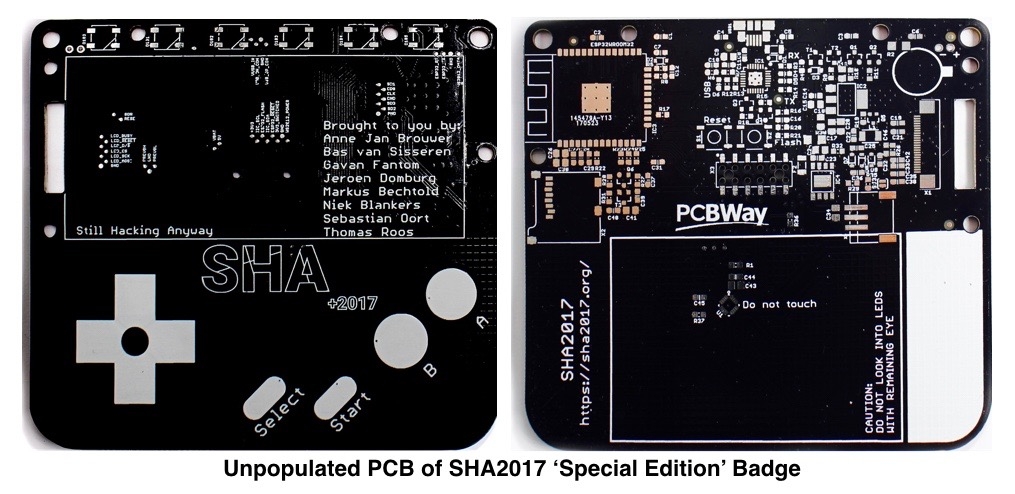
In events like these, people are given badges showing their name and professional affiliation. However, the team organizing SHA2017 wanted to create something special. The SHA2017 badge prototype is not meant to be just a reusable badge, and this is where Espressif’s contribution came in. The SHA2017 badge is interactive, and is based on the ESP32 technology, comprising a special version of the ESP-WROOM-32 module with a 128 Mbit flash and a 2.9” e-paper display (296×128 pixels) which makes the badge readable both in direct sunlight and at night. Not only will the badge show the holder’s basic information, but it will also provide details on the event’s timetable and even weather updates. More importantly, however, people attending SHA2017 will be able to write code for this badge, make hardware modifications/extensions, and ultimately make their own projects using MicroPython in an online environment. The badge is fully open-source, both hardware and software, and it will be distributed to all participants upon arrival.
-
2026.05.14Anthropic's recent Build with Claude event showcased the M5Stack Cardputer, powered by Espressif's ESP32-S3, as recommended development hardware for building AI Agent interfaces.
-
2026.05.08Users currently developing or producing with the ESP32-P4 should upgrade their firmware and hardware designs as soon as possible.
-
2026.04.10Espressif’s ESP32-C6 platform now supports Amazon’s Alexa Connect Kit SDK for Matter, giving device makers a new option for building feature-rich Alexa-enabled smart home products with Wi-Fi 6 connectivity, strong security, and greater design flexibility.
 LinkedIn
LinkedIn 微信
微信
 Twitter
Twitter Facebook
Facebook



